‘No Way To Prevent This,’ Says Only Package Manager Where This Regularly Happens
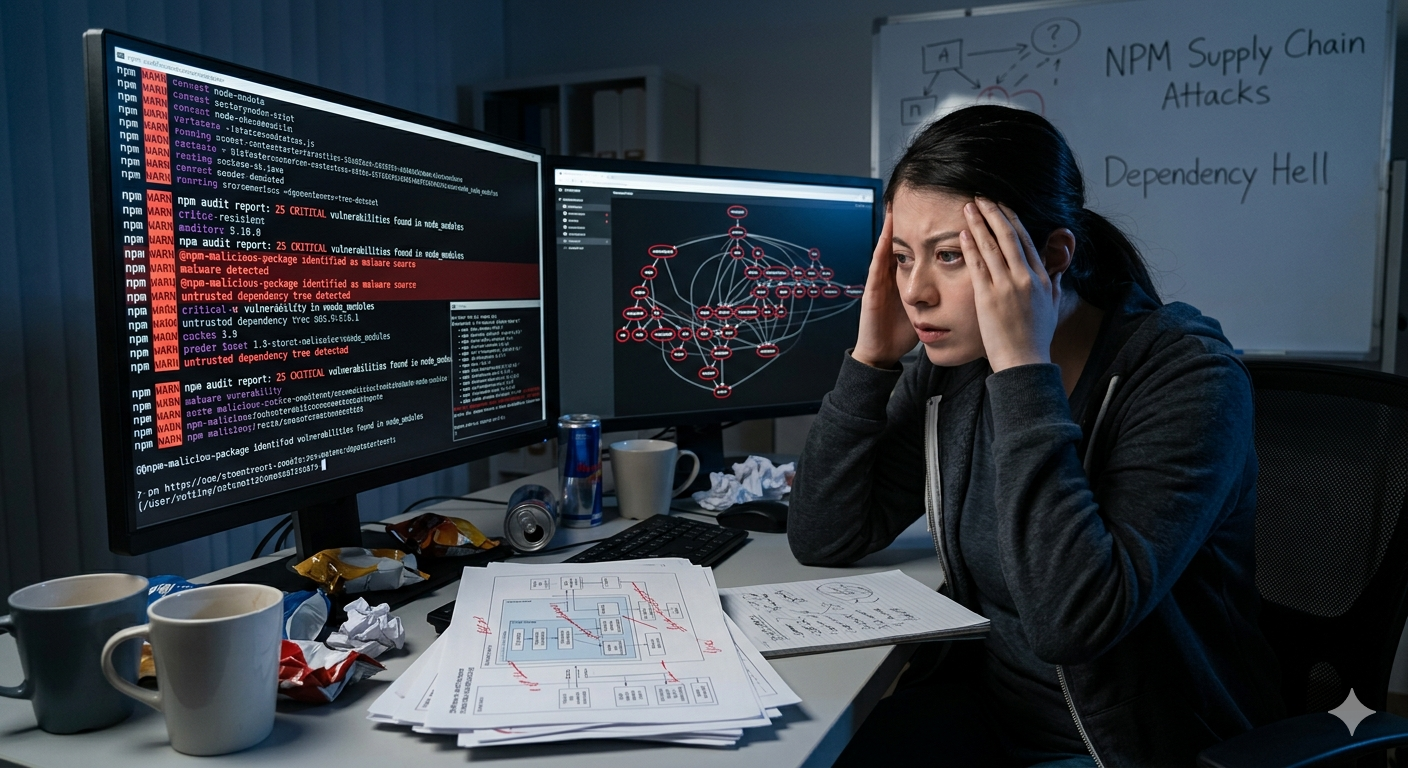
SAN FRANCISCO, CA - In the wake of a devastating supply chain attack in the npm registry that left millions of enterprise applications compromised and billions of user records exposed, developers across the JavaScript ecosystem expressed deep sorrow today, lamenting that such a crisis was completely unavoidable.
“It’s a shame, but what can you do? This is just the price of building modern web apps,” said Senior Frontend Engineer Mark Vance, echoing the sentiments of a community that completely relies on a 40-level-deep nested tree of unvetted packages maintained by pseudonymous strangers to capitalize a single string. “There’s absolutely no way to foresee or prevent someone from taking over a long-abandoned utility package and injecting a crypto-miner into every production build in the world. It’s just an act of nature.”
At press time, residents of the Node.js ecosystem stood unified in their belief that the malicious remote-code execution was a completely unpredictable tragedy, offering their thoughts and prayers to the DevOps teams currently scrambling to rotate their corporate AWS keys.
Interestingly, developers in ecosystems like Go, Rust, and those utilizing native Web APIs—where robust standard libraries drastically reduce reliance on third-party code and strict cryptographic verification is built into the core toolchain—reported zero instances of a college dropout’s weekend project wiping out global logistics infrastructure today.
“It’s devastating, but we have to accept that we live in a world where bad actors exist. There are no registry policies or build-sandbox guardrails we could possibly enforce to stop it,” said an npm spokesperson, standing in front of an open-source registry that happily executes arbitrary installation scripts on local machines by default. “Our hearts go out to the victims. Until the next inevitable breach tomorrow morning, we must simply remain resilient.”